- What is External MPI in 3DS authentication?
- Why does acquirer-managed 3DS limit payment orchestration?
- How does External MPI work before authorization?
- Which 3DS authentication artifacts matter for authorization?
- How does External MPI improve routing, cascading, and retries?
- How should payment teams decide when to trigger 3DS?
- How does External MPI support soft decline recovery?
- What are the compliance and risk implications?
- Where does Akurateco fit in the External MPI model?
- Implementation checklist for payment teams
- FAQ
- Conclusion
External MPI changes where 3DS authentication sits in the payment flow. Instead of letting each acquirer trigger authentication inside its own processing path, authentication is handled centrally before authorization.
That matters when your payment infrastructure depends on multiple acquirers, PSPs, routing rules, cascading, fraud controls, and regional optimization. In a single-acquirer setup, acquirer-led 3DS may be enough. In a multi-acquirer environment, it can become a constraint.
An External MPI model lets payment teams separate authentication from authorization. The result is a more flexible transaction lifecycle where 3DS authentication can support routing strategy instead of limiting it.
EMVCo describes EMV 3DS as a protocol that enables data exchange between merchants and issuers to authenticate consumers and reduce card-not-present fraud while avoiding unnecessary checkout friction. External MPI builds on that principle by placing the authentication layer inside the payment orchestration architecture rather than inside one acquirer’s infrastructure.
What is External MPI in 3DS authentication?
External MPI is an acquirer-independent 3DS authentication layer. It authenticates the cardholder before authorization and passes the resulting authentication data into the authorization request.
In traditional card-not-present payments, 3DS authentication is often handled inside the acquirer or gateway path. The merchant sends a transaction toward a specific acquirer, and that acquirer’s 3DS infrastructure manages the authentication flow.
External MPI changes that sequence. Authentication happens before the transaction is committed to a specific acquirer. Once the issuer completes authentication, the payment gateway or orchestration layer receives the authentication result and can include it in the authorization request.
This makes authentication a centralized service within the payment stack. It can be governed by merchant-level rules, issuer behavior, BIN logic, transaction risk, geography, and cascading strategy.
In modern 3DS terminology, the architecture usually involves a 3DS server, directory server, issuer Access Control Server, and authentication result data. “External MPI” is still widely used as a practical market term for an external merchant authentication layer that performs this function independently from a single acquirer.
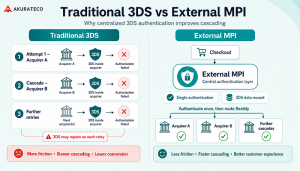
Why does acquirer-managed 3DS limit payment orchestration?
Acquirer-managed 3DS works in a linear payment flow, but it becomes restrictive when a merchant needs routing, cascading, retries, and centralized risk logic across several providers.
In a single-acquirer setup, authentication and authorization can remain tightly connected. The acquirer triggers 3DS, receives the result, and continues to authorization.
The problem appears when the merchant uses several acquirers. If authentication is tied to the first acquirer, a failed authorization may require the next attempt to repeat the authentication flow. That can create friction, slow down retries, and weaken cascading logic.
| Area | Acquirer-managed 3DS | External MPI model |
|---|---|---|
| Authentication location | Inside acquirer path | Before acquirer selection |
| Routing flexibility | Limited by selected acquirer | Controlled by orchestration layer |
| Cascading | May require repeated 3DS | Can reuse authentication data where supported |
| Customer experience | Multiple challenges possible | Single authentication flow preferred |
| Analytics | Fragmented by acquirer | Centralized across transactions |
| Risk control | Often acquirer-dependent | Merchant / orchestrator-defined |
The operational issue is not that acquirer-managed 3DS is technically wrong. It is that it was designed for a more linear model than many payment teams now operate.
For PSPs, fintech companies, and enterprise merchants, the payment flow is no longer just “checkout → acquirer → issuer.” It often includes risk checks, tokenization, routing, fallback acquirers, retries, settlement reporting, reconciliation, and performance monitoring. Authentication needs to fit that architecture.
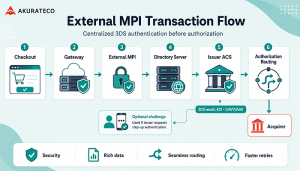
How does External MPI work before authorization?
External MPI moves 3DS authentication to the pre-authorization stage. The payment orchestration layer first authenticates the transaction, then selects the authorization route.
The flow starts when the customer enters card details and checkout context is collected. That context may include device data, billing and shipping details, transaction amount, currency, customer history, card BIN, country, and risk indicators.
The orchestration layer then decides whether 3DS authentication is needed. This decision may be based on regulation, fraud risk, issuer expectations, transaction value, merchant policy, or the probability that authentication will improve authorization success.
If authentication is required, the External MPI sends the authentication request through the 3DS ecosystem. The directory server identifies the relevant issuer, and the issuer’s ACS decides whether the transaction can be authenticated frictionlessly or requires a challenge.
Visa explains that 3DS enables data exchange between the merchant, issuer, and consumer where necessary to validate that the transaction is initiated by the rightful account owner before authorization.
| Stage | What happens | Systems involved | Operational risk |
|---|---|---|---|
| Checkout data collection | Card, device, customer, and transaction data are collected | Checkout, gateway, risk tools | Poor data quality can reduce frictionless rates |
| 3DS decision | System decides whether to trigger authentication | Gateway, risk engine, rules engine | Over-triggering creates friction |
| Authentication request | External MPI initiates 3DS flow | External MPI / 3DS server, directory server | Issuer timeout or technical failure |
| Issuer decision | Issuer approves frictionless or requests challenge | ACS, issuer risk systems | Challenge abandonment |
| Authentication result | ECI, CAVV/AAV, transaction IDs, version, status returned | External MPI, gateway | Missing data can break authorization |
| Authorization routing | Gateway selects acquirer and submits authorization | Gateway, acquirer, issuer | Route may not support external 3DS fields |
| Retry / cascade | Failed authorization can be retried through another acquirer | Orchestration layer | Must respect scheme and acquirer rules |
This architecture makes authentication part of payment strategy. It is no longer just a compliance checkpoint attached to one provider.
Which 3DS authentication artifacts matter for authorization?
The most important 3DS artifacts are the values that prove authentication occurred and allow the issuer and network to validate the transaction during authorization.
After 3DS authentication, the issuer and directory server return authentication data. The gateway includes the required fields in the authorization request, subject to card-network, acquirer, processor, and integration requirements.
| Parameter | Meaning | Why it matters |
|---|---|---|
| ECI | Electronic Commerce Indicator | Indicates authentication status and liability-shift context |
| CAVV / AAV | Cardholder / Accountholder Authentication Value | Cryptographic proof that issuer-side authentication was completed |
| DS Transaction ID | Directory server transaction identifier | Supports traceability across the 3DS flow |
| ACS Transaction ID | Issuer ACS reference | Helps issuer-side validation and troubleshooting |
| 3DS Version | Protocol version used | Confirms compatibility and expected data structure |
| Challenge Indicator / Result | Whether challenge occurred and its result | Helps measure friction and abandonment |
These fields are not just technical metadata. They influence authorization decisioning, issuer validation, dispute handling, and operational analytics.
The important caveat is that reuse depends on the downstream path. External MPI creates portability, but the acquirer, processor, network, and scheme configuration must support externally generated 3DS data in the authorization request.
How does External MPI improve routing, cascading, and retries?
External MPI lets the orchestration layer authenticate once, then route authorization dynamically. This can reduce repeated challenges and make cascading faster where external 3DS data is accepted.
Payment routing works best when the orchestration layer has freedom to select the most appropriate acquirer. That decision may depend on cost, geography, issuer behavior, BIN, currency, risk score, provider uptime, or historical approval performance.
Acquirer-managed 3DS weakens that freedom because authentication is attached to the first selected path. If that path fails, a second path may not be able to use the same authentication result.
External MPI improves the model by creating a reusable authentication result before authorization. When a transaction is authenticated centrally, the gateway can choose the best available authorization path and include the authentication artifacts in the request.
| Scenario | Traditional model | External MPI model |
|---|---|---|
| First authorization attempt | Acquirer triggers 3DS | Gateway authenticates before routing |
| First authorization fails | Retry may need new authentication | Gateway can route to another acquirer with existing 3DS data where supported |
| Cascading speed | Slower if 3DS repeats | Faster because authentication is already complete |
| Customer friction | Challenge may repeat | Challenge is minimized to one flow |
| Optimization | Provider-specific | Centralized across providers |
Akurateco’s payment orchestration platform already positions routing and cascading as core orchestration capabilities, including routing by cost, region, card type, and retrying declined transactions via alternative channels. External MPI extends the same orchestration logic to authentication.
How should payment teams decide when to trigger 3DS?
3DS should not be treated as an always-on switch. The best strategy is adaptive: trigger authentication when it is required, when risk is elevated, or when authentication is likely to improve authorization.
A centralized decision layer should evaluate multiple signals before triggering 3DS:
- Regulation and SCA requirements
- Transaction amount
- Card BIN and issuer behavior
- Customer country and merchant country
- Device and browser signals
- Customer history
- Merchant risk profile
- Product or industry risk
- Previous issuer soft declines
- Fraud-score thresholds
- Exemption eligibility
This is where External MPI becomes more than a technical 3DS component. It becomes part of risk governance.
For example, a low-risk returning customer with a familiar device may qualify for a frictionless path or exemption request. A high-value transaction from a new customer in a sensitive market may require step-up authentication. A specific issuer may have better approval behavior when 3DS data is provided, even if authentication is not strictly mandatory.
EMVCo notes that EMV 3DS enables issuers to use transaction, payment-method, and device data to assess risk and avoid unnecessary friction where possible. That makes data quality and routing logic critical.
How does External MPI support soft decline recovery?
External MPI can help recover authentication-related soft declines by triggering step-up authentication and retrying authorization with valid 3DS data.
A soft decline is not always a final refusal. In many cases, it means the issuer wants additional authentication or a different transaction condition before approving the payment.
In a conventional flow, the customer may simply see a failed payment and be asked to try again. That creates unnecessary abandonment.
With External MPI, the orchestration layer can interpret an authentication-related soft decline, trigger 3DS step-up authentication, receive the authentication artifacts, and retry the authorization. This creates a controlled recovery loop.
A practical recovery flow looks like this:
- Authorization is attempted without 3DS or with insufficient authentication context.
- Issuer returns an authentication-related soft decline.
- Gateway triggers External MPI authentication.
- Customer completes frictionless or challenge flow.
- Gateway retries authorization with authentication artifacts.
- If needed, the orchestration layer routes the retry through the most suitable acquirer.
This is especially useful for subscription businesses, high-risk verticals, marketplaces, and cross-border merchants where issuer behavior varies significantly.
What are the compliance and risk implications?
External MPI can help centralize SCA, exemption, and risk decisions, but payment teams still need to follow regional regulation, scheme rules, acquirer requirements, and privacy obligations.
For European and UK payment flows, 3DS is closely connected to Strong Customer Authentication. Stripe describes SCA as a regulatory requirement affecting many European online payments and notes that 3DS is commonly used to satisfy two-factor authentication requirements. EMVCo also states that EMV 3DS supports SCA by enabling two-factor authentication and allowing issuers to consider risk and regulatory factors when deciding how to authenticate the customer.
External MPI does not remove compliance complexity. It centralizes it.
That centralization can help payment teams apply consistent rules across acquirers:
| Compliance / risk area | Why it matters | How External MPI helps |
|---|---|---|
| SCA | Required for many regulated transactions | Centralizes authentication decisioning |
| Exemptions | Low-risk transactions may avoid challenge | Applies exemption logic consistently |
| Fraud control | Issuers need enough data for risk decisions | Improves data collection and routing context |
| Privacy | 3DS uses customer and device data | Keeps governance in one architecture |
| Auditability | Payment teams need traceability | Centralizes authentication logs and outcomes |
| Dispute handling | Authentication status can affect liability | Preserves relevant authentication evidence |
The practical benefit is governance. Instead of having each acquirer apply authentication differently, the payment team can design a single strategy and apply it across the payment stack.
Where does Akurateco fit in the External MPI model?
Akurateco can position External MPI as part of an orchestration-first payment architecture: authentication, routing, cascading, fraud rules, and analytics work together instead of being managed separately.
Akurateco’s broader product positioning already fits this topic. Its payment orchestration platform connects multiple providers, supports smart routing and cascading, and centralizes payment operations through a single layer. Its intelligent routing page also highlights routing by BIN, card brand, currency, region, transaction amount, and smart retry logic for soft-declined transactions.
External MPI strengthens that architecture by adding centralized authentication governance before authorization.
For PSPs and fintech companies, this means they can offer merchants a more controlled 3DS strategy without hard-binding authentication to one acquirer. For enterprise merchants, it means the payment team can manage authentication, routing, and retries from one operating model.
Akurateco’s value angle should not be “3DS as a feature.” It should be “3DS as an orchestrated layer of payment performance.”
That positioning connects naturally to:
- Multi-acquirer infrastructure
- Approval-rate optimization
- Smart routing
- Cascading
- Soft decline recovery
- Fraud and risk controls
- Payment analytics
- Merchant reporting
- Faster infrastructure scaling
Implementation checklist for payment teams
External MPI requires more than connecting a 3DS provider. Payment teams must confirm data quality, acquirer support, routing logic, risk rules, analytics, and failure handling.
Before implementing External MPI, payment teams should validate the following:
| Area | Questions to answer |
|---|---|
| Acquirer support | Can each acquirer accept externally generated 3DS data? Which fields are required? |
| Network rules | Are the relevant schemes and regions supported for the intended flow? |
| Data collection | Is checkout collecting enough device, browser, customer, and transaction data? |
| Routing logic | Can the gateway route after authentication without losing 3DS context? |
| Cascading rules | Which decline codes should trigger retry, cascade, or step-up authentication? |
| Exemptions | Which exemptions are supported, and who decides when to request them? |
| Challenge UX | Is the challenge flow optimized for web, mobile, and hosted checkout? |
| Webhooks | Are authentication, challenge, decline, retry, and final status events visible? |
| Monitoring | Can the team track frictionless rate, challenge rate, abandonment, issuer behavior, and latency? |
| Reconciliation | Can authentication results be connected to authorization, settlement, disputes, and reports? |
The most common mistake is treating External MPI as a standalone security component. It should be implemented as part of the full transaction lifecycle.
FAQ
What is External MPI in payments?
External MPI is an acquirer-independent 3DS authentication layer. It performs cardholder authentication before authorization and returns authentication data such as ECI, CAVV or AAV, DS Transaction ID, ACS Transaction ID, and 3DS version. The gateway can then include this data in the authorization request.
How is External MPI different from acquirer-managed 3DS?
Acquirer-managed 3DS happens inside a specific acquirer’s processing path. External MPI moves authentication into the payment orchestration layer before acquirer selection. This gives payment teams more control over authentication rules, routing logic, cascading, retries, issuer analysis, and fraud strategy across multiple providers.
Can 3DS authentication results be reused across acquirers?
Yes, but only where the acquirer, processor, card network, and integration setup support externally generated 3DS authentication data. External MPI makes authentication data portable at the orchestration level, but downstream systems must be able to receive and process the required authentication fields correctly.
How does External MPI help with soft declines?
External MPI can help recover authentication-related soft declines by triggering step-up 3DS authentication after the issuer requests stronger verification. Once the customer completes authentication, the gateway can retry authorization with valid 3DS data and, if needed, route the transaction through another supported acquirer.
How can payment orchestration help with External MPI?
Payment orchestration connects External MPI with routing, cascading, fraud rules, retries, analytics, and reporting. Instead of treating authentication as a separate compliance step, the orchestration layer uses 3DS data as part of the full payment strategy, helping payment teams improve control and operational visibility.
Conclusion
External MPI is most useful when payment infrastructure has outgrown linear processing. If your business depends on several acquirers, routing logic, retry flows, and issuer-specific performance patterns, authentication should not be locked inside a single processing endpoint.
The practical decision framework is straightforward: if 3DS affects authorization success, customer friction, soft decline recovery, or routing flexibility, it should be governed centrally.
For PSPs, fintech companies, and enterprise merchants, External MPI turns authentication into a controllable infrastructure layer. It supports stronger risk management, cleaner cascading, better retry logic, and more consistent operational visibility.
For companies managing complex payment infrastructure, Akurateco can act as a technology partner that helps simplify orchestration, routing, provider connectivity, fraud controls, reporting, and scalability without requiring a full infrastructure rebuild.