- What Does P2PE Mean, and What Does It Stand For?
- How P2PE Works in a Card-Present Payment Flow
- P2PE vs. End-to-End Encryption vs. TLS
- What Is a PCI-Validated P2PE Solution?
- What Is P2PE Compliance, and How Does It Relate to PCI DSS?
- What Is a P2PE Terminal, and Why Is a Terminal Alone Not Enough?
- How to Verify Your P2PE Solution
- P2PE Implementation Playbook: How to Keep a P2PE Setup Secure
- How Akurateco Fits Into a PCI-Efficient Omnichannel Stack
- Where Teams Get P2PE Wrong: Common Mistakes to Avoid
- Conclusion
- FAQ
When businesses evaluate payment security, they often assume that if card data is encrypted somewhere in the process, the risk is under control. In reality, card-present security is rarely that simple. Exposure often begins much closer to the point of sale — at the terminal, in the store environment, or in the systems surrounding the payment flow. That is why so many teams start asking what is P2PE and whether their setup protects card data at the moment of capture, not just later in transit.
P2PE, or point-to-point encryption, is a PCI-defined security method that encrypts payment card data at the point of interaction, such as a payment terminal, and keeps it unreadable until it reaches a secure decryption environment. In practice, P2PE helps reduce card data exposure in merchant systems and can simplify PCI DSS compliance when a PCI-listed P2PE solution is used.
While P2PE helps protect card data at the point of capture, Akurateco’s payment orchestration platform helps unify routing, reporting, provider management, and broader payment operations across omnichannel flows.
In this guide, we explain what P2PE means, how it works, how PCI validation differs from generic encryption, and what it changes for the PCI DSS scope.
What Does P2PE Mean, and What Does It Stand For?
At first glance, P2PE can sound like just another payments acronym. But the idea behind it is simple and important: card data should be protected from the very moment it is captured, not only somewhere later in the payment flow.
That is what point-to-point encryption is about. When a customer taps, inserts, or swipes their card, the data is encrypted at that point and stays unreadable until it reaches the secure environment that is allowed to decrypt it. The goal is to reduce how much usable card data exists in the merchant environment in the first place.
This is why P2PE should not be confused with a broad statement like “we encrypt payments.” PCI SSC defines it much more precisely: payment account data is protected from the point it is captured in the merchant’s payment device to the point it is decrypted in a solution or component provider’s environment.
So the real takeaway is that P2PE is a structured security model designed to reduce exposure where card-present risk actually begins: at the moment of capture.
How P2PE Works in a Card-Present Payment Flow
A simple way to understand what is P2PE payment is to follow the path of the data.
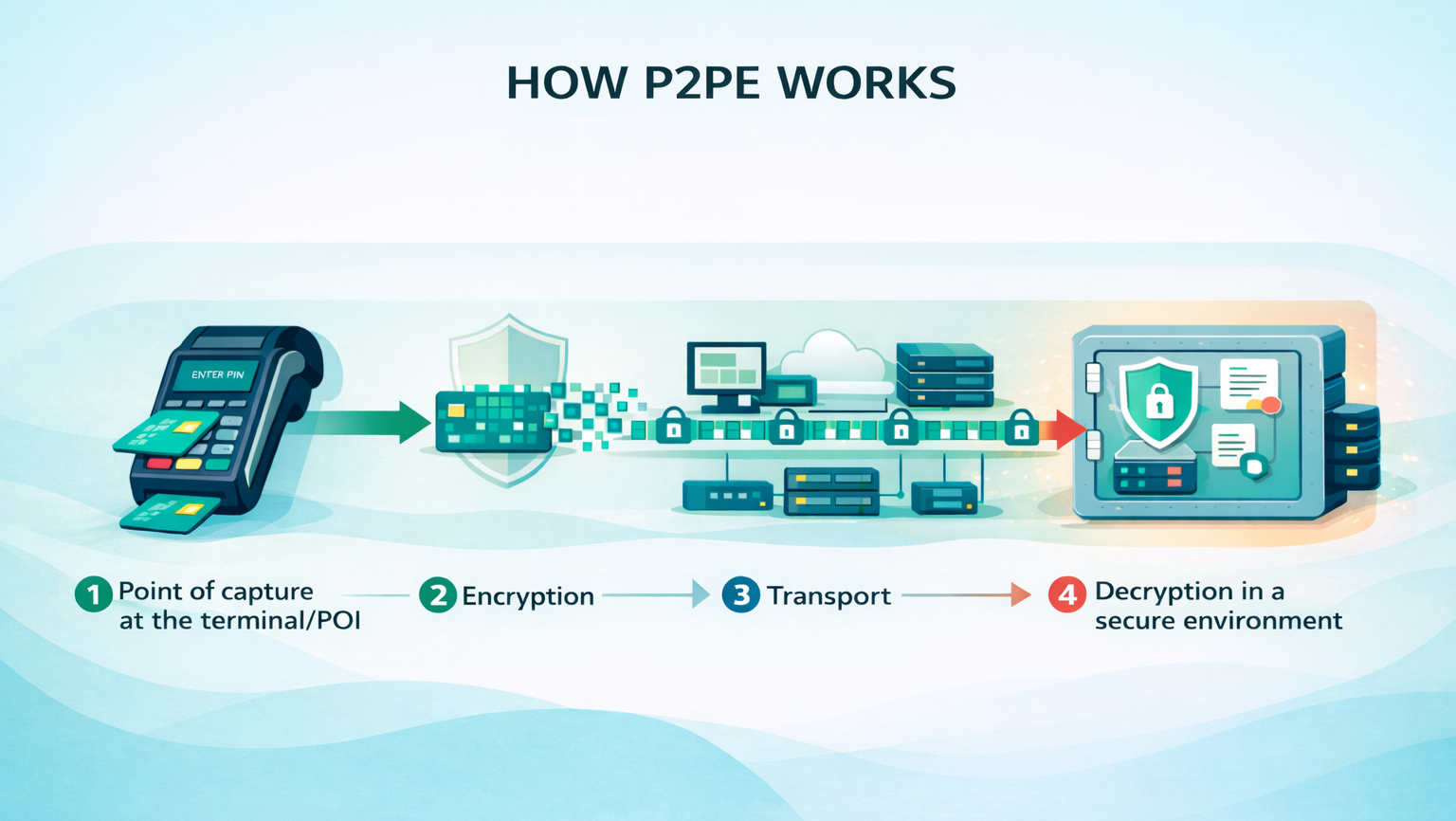
- A customer taps, inserts, or swipes their card at the point of interaction (POI) device, or payment terminal.
- The account data is captured there and encrypted immediately.
- From that moment on, it moves through merchant-side systems and networks in unreadable form.
- The data is only decrypted when it reaches the secure decryption environment.
This is what makes P2PE so valuable in card-present payments. If an attacker gains access to systems somewhere along that route, the stolen data is far less useful because it is not exposed in clear text between capture and decryption. PCI SSC directly links that unreadable state to a lower breach value.
P2PE vs. End-to-End Encryption vs. TLS
Many teams assume these terms are interchangeable. But in reality, they are not.
Approach | What It Protects | Where Clear-Text Data May Still Exist | What “Validated” Means |
| P2PE | Payment account data from capture at the POI to the secure decryption environment | Exposure is minimized between the PCI-approved POI and the decryption point when the full solution is PCI-listed | A PCI-listed or PCI-validated solution assessed against the PCI P2PE Standard |
End-to-end encryption (E2EE) | Data between two endpoints, depending on how a vendor defines those endpoints | Clear-text may still exist depending on endpoint placement, device design, or decryption handling | “E2EE” alone is not a PCI SSC P2PE validation status |
| TLS | Data in transit between communicating systems | Clear-text can still exist before TLS starts, after it terminates, or inside connected systems | TLS is a transport protocol, not a PCI P2PE validation model |
Only PCI-listed P2PE maps to PCI SSC’s language about secure decryption, listed solutions, and fewer applicable PCI DSS requirements for merchants using those listed solutions. TLS still matters, but it solves a different problem. It protects traffic between systems, not the full card-present security model that PCI SSC defines for P2PE.
What Is a PCI-Validated P2PE Solution?
This is the part that matters most when comparing vendors.
When businesses search what is P2PE solution or try to understand what is PCI SSC validated P2PE solution, they should think beyond a terminal or an encrypted connection. According to PCI SSC’s “At a Glance” guidance, a PCI-listed P2PE solution includes secure devices, applications, and processes that work together to encrypt cardholder data from a PCI-approved point-of-interaction device through to a secure decryption environment.
Another key point is that the PCI P2PE Standard defines requirements and test procedures for providers and vendors that protect payment card data. PCI SSC states this directly in its FAQ. That is why “validated” means more than simply “encrypted.” It points to a defined standard and an assessment model, not just a product feature described by a vendor.
Two clarifications are especially important.
First, validated P2PE components (not sufficient alone) are not the same as a validated end-to-end solution. PCI SSC explains that a P2PE component is only part of a broader P2PE service and is intended to be used within a full P2PE solution. On its own, a component does not mean a business is using a validated P2PE solution.
Second, PCI SSC encourages merchants, acquirers, and solution providers to use the PCI SSC listings when selecting P2PE solutions, components, and applications. But the listing should be treated as a verification resource, not as a shortcut around due diligence. A solution being listed is important, but it does not remove the need to confirm status, scope, responsibilities, and the way the solution is actually deployed.
What Is P2PE Compliance, and How Does It Relate to PCI DSS?
When buyers ask what is P2PE compliance or what is PCI P2PE, they are usually asking whether P2PE replaces PCI DSS. It does not. P2PE is a PCI SSC standard and program for protecting payment account data from capture to decryption in card-present flows. PCI DSS is the broader security framework for systems that store, process, transmit, or can affect the security of cardholder data.
What P2PE can do is simplify the merchant side of compliance. PCI SSC says merchants using PCI-listed P2PE solutions have fewer applicable PCI DSS requirements, helping simplify compliance efforts. That is the safest way to describe the benefit. It supports the idea of reduced PCI DSS requirements (for merchants using PCI-listed P2PE), but it does not support saying that PCI obligations disappear.
Merchants still need to secure any remaining in-scope systems, follow their acquirer’s program rules, and understand their broader compliance posture. For readers who want that wider PCI context, Akurateco’s guide on who needs to be PCI compliant is a useful guide to rely on, and its breakdown of the PCI DSS cost helps frame the budgeting side of the decision.
What Is a P2PE Terminal, and Why Is a Terminal Alone Not Enough?
A P2PE terminal is the payment terminal, or point-of-interaction (POI) device, where card data is captured during an in-person transaction. It is the device a customer uses to tap, insert, or swipe their card at checkout.
On its own, though, a terminal is not the same as P2PE. A device only becomes part of a validated setup when it is used within a PCI-listed P2PE solution that includes the required applications, key management, secure decryption environment, and operating procedures. In other words, a terminal by itself does not mean a business is using validated P2PE.
This is also where phrases like what is an approved P2PE or what is an approved P2PE can cause confusion. The more accurate industry term is a PCI-listed or PCI-validated P2PE solution. What needs to be verified is the full solution listing, not just the terminal itself or a broad claim that the payment data is encrypted.
How to Verify Your P2PE Solution
A P2PE setup is only as strong as the way it is selected, verified, and managed. Before relying on vendor claims, merchants and payment teams should confirm that the solution is listed, current, and aligned with their actual devices and processes.
Solution name on the PCI SSC listing
Start by checking the exact solution name on the PCI SSC P2PE Solutions listing. PCI SSC presents that listing as a resource for merchants and acquirers selecting a validated P2PE solution. It also helps distinguish active listings from expired ones, which makes outdated claims easier to spot.
P2PE instruction manual (PIM)
Next, confirm that you have the P2PE instruction manual (PIM) for the listed solution. PCI SSC states that each PCI-listed P2PE solution has an associated PIM. The manual helps merchants securely manage the devices and environment under their control, including installation, device monitoring, tamper awareness, and incident response.
Validation status and supported devices
Then review the solution’s current status and supported device models at a high level. Make sure the solution is still validated, not expired, and that the devices you use are actually covered by that listing.
Responsibility split across all parties
Finally, confirm who is responsible for what. That may include the merchant, the solution provider, and, where relevant, the reseller, installer, or integrator. This split is easy to overlook, but it often becomes critical during audits, store rollouts, or device-related incidents.
P2PE Implementation Playbook: How to Keep a P2PE Setup Secure
A P2PE setup is not only about encryption. It also depends on how devices are deployed, tracked, checked, and handled in daily operations.
Rollout planning across stores and devices
Start with rollout planning. That means thinking through stores, lanes, terminal models, delivery paths, and replacement workflows before devices go live. Even a strong technical setup can break down if devices are deployed inconsistently or move through weak handoff and control processes.
Device inventory and replacement control
Accurate device inventory is just as important. Teams should know which terminal is deployed in each location, how it is identified, and how replacements, returns, and swaps are handled. This helps during audits and also reduces confusion when a device is missing, looks suspicious, or needs to be replaced quickly.
Store staff procedures and tamper awareness
Store staff also need clear procedures. They should know how to inspect devices, what signs may indicate tampering, and when to escalate concerns instead of continuing to use the terminal. PCI SSC treats this as part of secure device management, not as an optional extra.
Incident response when a device looks suspicious
Finally, teams need a basic response plan for suspicious devices. If a terminal appears damaged, altered, or out of place, staff should know how to stop using it, report it internally, and follow the provider’s guidance. P2PE works best when the operating model around the devices is as disciplined as the encryption itself.
How Akurateco Fits Into a PCI-Efficient Omnichannel Stack
Akurateco’s role in this setup is clear: it acts as the orchestration and management layer, not as the P2PE solution itself.
According to the Akurateco FAQ, the platform is PCI DSS Level 1 certified. The same FAQ explains that clients using the SaaS version are covered by that certification, while clients deploying the platform on-premise on their own servers should obtain PCI DSS certification separately. Akurateco also states that it can support those on-premise clients with the documents and instructions needed for the QSA process.
In practice, this creates a logical split of responsibilities. A PCI-listed P2PE solution protects card-present data at the point of capture. Akurateco’s payment orchestration platform then helps centralize routing, reporting, and multi-provider payment operations across channels. At the same time, tokenization can support safer handling of sensitive payment data in adjacent online or recurring-payment flows.
Together, this gives merchants and PSPs a cleaner way to connect in-person and online payment operations without confusing card-present data protection with broader payment orchestration responsibilities.
Where Teams Get P2PE Wrong: Common Mistakes to Avoid
Most P2PE misunderstandings do not come from the technology itself. They come from assumptions made during vendor evaluation, rollout, or compliance planning. These mistakes seem small at first, but they often lead to the biggest gaps later.
Treating “encrypted” as the same thing as PCI-validated P2PE
This is the most common mistake. A vendor may say that payment data is encrypted, but that alone does not mean the setup qualifies as PCI-validated P2PE. The important question is not whether encryption exists somewhere in the flow. It is whether the full solution is validated and listed under the PCI SSC program.
Assuming the terminal alone proves you “have P2PE”
A payment terminal can be part of a P2PE setup, but it is not proof by itself. A device only counts within a PCI-listed P2PE model when it is used as part of the full validated solution. If buyers stop at the terminal spec sheet, they can miss the bigger requirement: the listing applies to the complete solution, not to the hardware alone.
Overlooking the PIM and day-to-day device procedures
P2PE is not only about how data is encrypted. It is also about how devices are handled in real life. The P2PE Instruction Manual (PIM) matters because it guides merchants on installation, monitoring, tamper awareness, and device management. Ignoring those procedures weakens the value of the setup, even if the technical architecture looks strong on paper.
Treating P2PE as a replacement for broader PCI responsibilities
P2PE can reduce exposure and simplify compliance efforts, but it does not replace the broader PCI program. Merchants still need to understand what remains in scope, what responsibilities they still own, and how their wider payment environment is managed. This is where many teams get caught off guard during audits or implementation reviews.
Conclusion
P2PE matters because it protects payment account data at the point where card-present risk actually begins: the moment the data is captured. By keeping that data unreadable until it reaches the secure decryption environment, P2PE helps reduce exposure in the merchant environment. For merchants using PCI-listed P2PE solutions, it can also mean fewer applicable PCI DSS requirements and a more manageable compliance effort.
Just as importantly, P2PE should be understood for what it is: a defined security model, not a generic encryption claim, not a terminal feature on its own, and not a replacement for broader PCI responsibilities. The real value comes from choosing a PCI-listed solution, verifying it properly, and supporting it with the right operational controls.
For businesses building a modern omnichannel payment setup, the strongest approach is to pair a PCI-listed P2PE solution for in-person acceptance with an orchestration layer like Akurateco that helps unify routing, reporting, and provider management across channels.
FAQ
What is P2PE?
P2PE is point-to-point encryption for payment account data in a card-present flow. PCI SSC says it protects account data from the point where the merchant accepts the payment card to the secure point of decryption, and that the data remains unreadable until it reaches the secure decryption environment. That is why P2PE is more than a generic encryption feature. It describes a specific security model for protecting card-present data.
What does P2PE stand for?
The core P2PE meaning stands for point-to-point encryption. The name reflects the path of the protected data, from the point of interaction where the card is accepted to the secure environment where decryption is allowed. In practical terms, it means the merchant-side path between those points is designed so the data stays unreadable. That is the core meaning behind searches like “what is P2PE meaning.”
What is P2PE encryption?
Point to point encryption is not just any encryption used in payments. PCI SSC says the P2PE Standard contains detailed security requirements and testing procedures for application vendors and providers of P2PE solutions to protect payment card data. So the important idea is not only that data is encrypted, but that the solution is structured and assessed under a recognized PCI program. That is what makes the term meaningful in compliance and vendor selection.
What is a P2PE payment?
A P2PE payment is a card-present payment flow where the account data is encrypted at capture and stays unreadable until it reaches the secure decryption environment. This matters because it reduces the usefulness of stolen data if systems along the route are compromised. PCI SSC explicitly says that unreadable account data is less valuable if stolen in a breach. That is one of the main reasons merchants use P2PE in retail and hospitality environments.
What is a PCI-validated P2PE solution?
It is a PCI-listed solution that has been assessed against the PCI P2PE Standard. PCI SSC’s “At a Glance” document says a PCI-listed P2PE solution includes secure devices, applications, and processes that encrypt cardholder data from a PCI-approved POI device through to a secure decryption environment. That means the validation belongs to the full solution, not just to a terminal or one component inside the stack. Buyers should always verify the exact listing.
What is P2PE compliance?
P2PE compliance refers to alignment with the PCI SSC P2PE standard and listing model, not to PCI DSS as a whole. PCI SSC says merchants using PCI-listed P2PE solutions have fewer applicable PCI DSS requirements, which helps simplify compliance efforts. That is a real benefit, but it is not the same as saying all PCI obligations disappear. You still need to manage the remaining scope correctly.
What is a P2PE terminal?
A P2PE terminal is the payment terminal or POI device used inside a P2PE payment flow. But the device itself is not enough to prove that you “have P2PE.” It must be part of the full PCI-listed solution, together with the proper applications, decryption model, and operating procedures. If a vendor points only to the hardware, that is not the full answer.
What is my P2PE solution?
The best way to answer that is through verification. Check the exact solution name on the PCI SSC listing, confirm its status, and obtain the associated PIM. Then make sure your deployed devices and store procedures match the listed solution’s requirements. If one of those pieces is missing, your answer may be weaker than you think.
Does a P2PE component alone mean we “have P2PE”?
No. PCI SSC says a P2PE component is meant for use as part of a P2PE solution and that use of a component on its own does not constitute use of a validated P2PE solution. This is one of the most important clarifications in the whole topic because it prevents false confidence. Components matter, but the validated claim belongs to the full solution context.
Does P2PE eliminate PCI DSS obligations?
No. P2PE can simplify PCI work, but PCI SSC describes the benefit as fewer applicable PCI DSS requirements for merchants using PCI-listed solutions, not as total elimination of PCI responsibilities. Merchants still need due diligence, correct device handling, and a clear understanding of what remains in scope. That is why verification and operations matter as much as architecture.