- What Does PCI Cost Include?
- What Determines PCI Cost in the First Place?
- SAQ vs. ROC: The Path That Changes Your Budget Most
- Cost Breakdown: What You Actually Pay For
- Example Budgets: 4 Real-World Planning Scenarios
- How to Reduce PCI DSS Cost Without Lowering Security
- PCI DSS 4.x Budget Impacts You Shouldn’t Miss
- Practical Checklist: Estimate Your PCI Cost in 30 Minutes
- Conclusion
- FAQ
The short answer is that PCI is not a single fee. The real PCI DSS cost is a stack: validation, security tooling, testing, remediation, and the internal time needed to keep controls running all year. It is an ongoing security and governance investment that you must plan cautiously.
In 2026, budgeting also needs to reflect the realities of PCI DSS v4.0.1 and the future-dated requirements that became mandatory after March 31, 2025. In other words, PCI is not just an audit bill. It is an ongoing security and governance investment.
The good news is that PCI cost can often be reduced without compromising security, especially when scope and architecture are addressed early. Akurateco helps businesses move in that direction with PCI-ready white-label payment gateway infrastructure and a payment orchestration platform that supports a cleaner payment architecture and a lower compliance burden.
In this article, we look at the main cost drivers behind PCI DSS and how businesses can plan for them more effectively.
What Does PCI Cost Include?
When founders ask about the cost to be PCI compliant, they usually mean “What should I put into next year’s budget?” The useful answer is to split spending into four buckets:
- Validation: SAQ or ROC work, documentation, evidence collection, and packaging.
- Security controls: Logging, access control, hardening, encryption, MFA, and vulnerability management processes.
- Testing: Quarterly scans, annual penetration tests, and retesting after remediation.
- People and time: Engineering hours, compliance management, vendor follow-up, and recurring reviews.
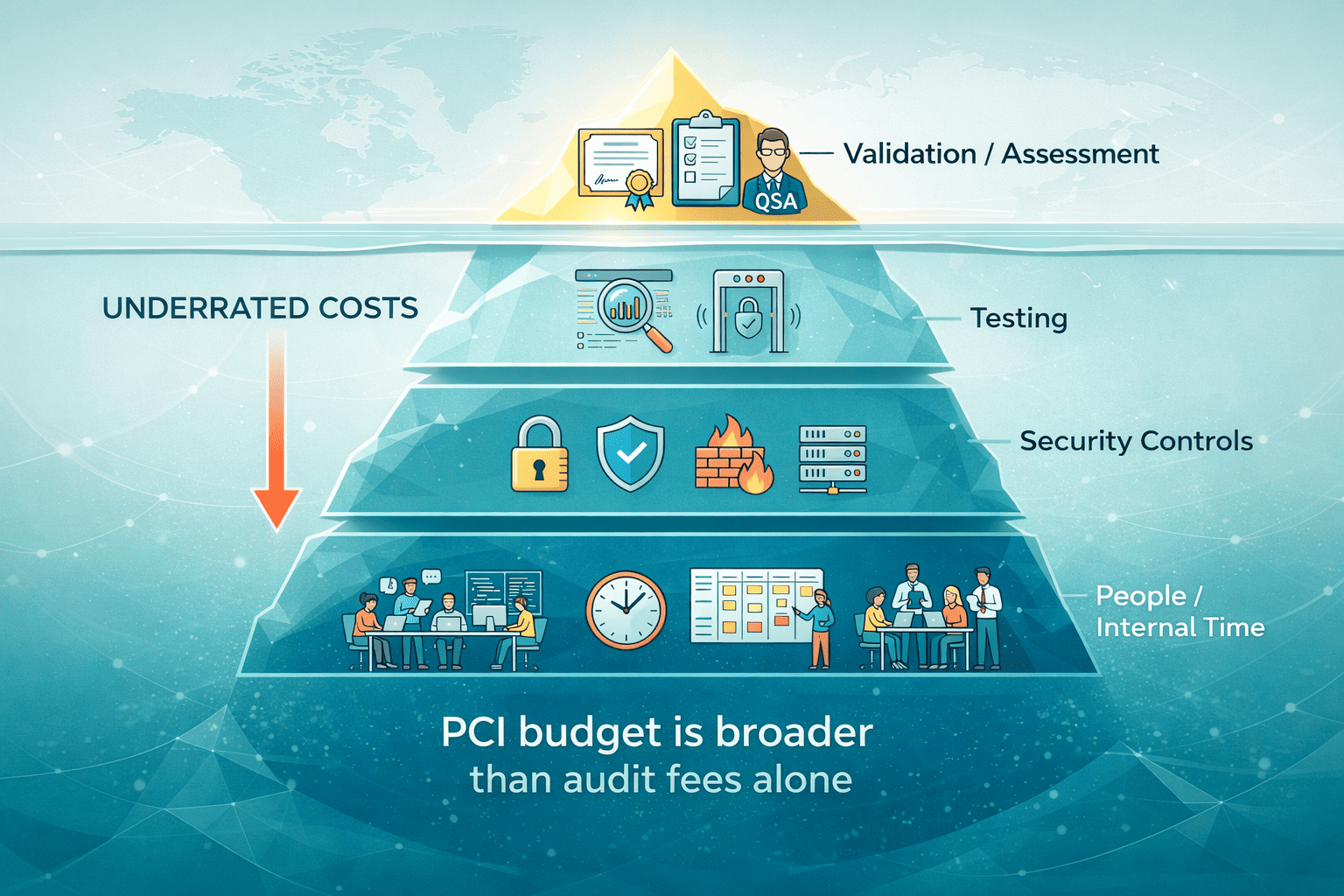
This model is useful because it shows why PCI DSS compliance is rarely just an audit expense. Validation and assessment are the visible parts, but the larger budget usually sits below the surface in security tooling, recurring testing, remediation work, and the time internal teams spend keeping controls in place. As the scope expands, each of those layers tends to grow, which is why PCI cost rises with complexity, not just with the price of the assessment.
What Determines PCI Cost in the First Place?
There is no universal PCI price tag because compliance cost depends on the shape of your payment environment. Budget is influenced by how much of the payment flow sits inside your own systems, how broad your scope is, which validation route applies, and how mature your security controls already are. In most cases, PCI becomes expensive not because of one audit fee, but because complexity spreads across infrastructure, testing, evidence, and remediation.
1. Scope size
The fastest predictor of PCI compliance cost is scope. The more systems, users, cloud services, domains, integrations, and vendors that touch payment flows, the more controls you need to implement, test, and evidence.
This is why scope creep is so expensive. A team starts with one checkout flow, then adds customer support access, BI exports, shared infrastructure, and new vendors. Suddenly, the payment footprint is wider than expected, and the audit burden grows with it.
2. Your payment architecture
E-commerce merchants, subscription platforms, PSPs, and large processors do not budget the same way. A small merchant using a hosted payment page often has a very different validation path from a PSP that manages routing logic, stores tokens, or operates multiple payment-facing environments.
PCI SSC also warns that SAQ A eligibility depends on how the payment page is actually delivered to the browser. If merchant-supplied elements are involved in collecting or processing card data, SAQ A may not apply.
3. Validation path: SAQ vs. ROC
This is the line item that can change the cost by an order of magnitude. SAQ-based validation is usually lighter and cheaper. A formal Report on Compliance (ROC) led by a Qualified Security Assessor (QSA) is heavier, slower, and more evidence-intensive. Public market guides often quote SAQ help in the tens to low thousands of dollars, while QSA-led assessments can run into the tens of thousands or more.
4. Control maturity
Two companies with the same transaction volume can have very different budgets. One already has logging, asset inventory, policy governance, and ticket-driven change control. The other still needs to build those basics. The second company pays more in consulting, tooling, and delay.
5. PCI DSS v4.x requirements that hit web teams
For some e-commerce teams, the biggest new budget impact is client-side payment-page security. PCI SSC says Requirements 6.4.3 and 11.6.1 focus on authorizing scripts, verifying their integrity, and monitoring for tampering on payment pages and related security-impacting headers. That often means new tooling, process changes, and more evidence collection.
SAQ vs. ROC: The Path That Changes Your Budget Most
Many founders mistakenly search for the phrase PCI DSS certification cost first. In practice, the biggest budget question is not “certification” as a single purchase. It is whether you are validating through a Self-Assessment Questionnaire (SAQ) or a Report on Compliance (ROC).
| Validation path | Who typically uses it | What it includes | Main cost drivers |
| SAQ | Many lower-complexity merchants and service providers that are eligible to self-assess | Questionnaire completion, internal review, evidence gathering, and attestation of compliance (AOC) submission as requested | External help, wrong SAQ selection, poor evidence, hidden scope, vendor follow-up |
| ROC | Level 1 merchants, many larger service providers, and some more complex environments | Formal assessment led by a qualified security assessor (QSA), detailed testing, interviews, sampling, evidence review, ROC report, and related AOC output | Multi-environment scope, weak documentation, shared infrastructure, high transaction volume, and remediation backlog |
PCI SSC’s current materials describe SAQs for PCI DSS v4.0.1 as validation tools for SAQ-eligible entities, and ROC templates are maintained separately for QSA-led assessments. Public market ranges cited by IXOPAY put SAQ assistance at around $50 to $10,000, and QSA/ROC work at around $15,000 to $100,000, depending on complexity.
Here is the practical takeaway: SAQ cost is not always cheap. It is cheap only when the scope is truly small, the evidence is easy to gather, and your architecture has already kept card data away from most of your stack.
Cost Breakdown: What You Actually Pay For
PCI DSS cost is made up of several layers, not one flat fee. Beyond the assessment itself, companies pay for documentation, testing, remediation, and the ongoing operational work needed to prove controls remain effective. The biggest budgeting mistake is focusing only on audit fees while underestimating the technical and internal costs around them.
Validation and documentation
This is the paperwork layer, but it still consumes real budget. It includes SAQ work, evidence gathering, and AOC packaging, such as selecting the right SAQ type, reviewing service-provider documents, collecting screenshots and exports, and assembling the supporting compliance evidence.
For Level 1 merchants and some Level 2 contexts, validation may require a QSA-led audit and Report on Compliance (ROC) instead of self-assessment. That usually makes this cost category significantly heavier in terms of time, documentation, and assessor involvement.
Typical public market range:
- SAQ support: $50-$10,000
- QSA/ROC assessment: $15,000-$100,000
This cost spikes when:
- You are unsure which SAQ applies
- Your vendors cannot provide clear compliance artifacts
- Your controls exist but are not documented
- Your internal teams need multiple rounds to assemble evidence
Security testing
For many merchants, the first recurring external fee is the Approved Scanning Vendor (ASV) scan cost. PCICompliance.com says ASV scans typically cost $100-$500 per quarter, while SecurityMetrics currently lists a quarterly ASV product at $150.
That means a basic annual scan budget often starts around $400-$2,000 annually, before any consulting support. You pay this only when your internet-facing systems are actually in scope. Some fully hosted checkout models may not need quarterly ASV scans, depending on architecture and acquirer expectations.
The other common testing line item is penetration testing cost. A typical consulting range is of $5,000-$30,000 per test. In reality, the price climbs when you have multiple applications, APIs, environments, mobile surfaces, or a large external attack surface.
Remediation and hardening
This is where budgets usually get blown. Remediation costs include patching, reconfiguration, replacing legacy components, tightening access, fixing logging gaps, improving secrets handling, and redesigning payment flows.
Remediation is often mistakenly described as a major swing factor, with examples ranging from hundreds or low thousands to much larger projects, depending on the gaps found. In reality, this is often the biggest variable because it reflects your architecture debt, not just compliance activity.
Operational forever costs
This is the part many teams miss in year-one planning. PCI is not finished after the assessment. You still need:
- Access reviews
- Policy updates
- Evidence retention
- Vendor management
- Recurring testing
- Log review and response
- Evidence that controls stayed in place
Under v4.x, web merchants may also need a budget for script inventories, ownership records, integrity checks, evidence of e-commerce script integrity controls, plus monitoring for tampering.
Example Budgets: 4 Real-World Planning Scenarios
The ranges below are a planning model, not a guaranteed quote. They are inferred from public market ranges for SAQ support, QSA/ROC work, ASV scans, pen tests, and common implementation patterns, then adjusted for scope and internal labor. Final requirements depend on your acquirer, payment-brand program, and architecture.
| Scenario | Typical annual range | What is usually included | What usually moves the number |
| Small e-commerce using a hosted payment page | $1,000-$15,000 | SAQ work, policy/evidence effort, light tooling, maybe no ASV if scope is truly outsourced | Wrong SAQ assumptions, weak website controls, outside help |
| SaaS business with card-on-file and tokenization | $10,000-$40,000 | SAQ or limited assessor help, scans where applicable, annual pen test, logging, vendor review | More systems in scope, token vault design, and customer portal complexity |
| Mid-size merchant with multiple environments | $25,000-$90,000 | SAQ or assessor support, quarterly scans, annual pen test, stronger monitoring, more remediation | Shared infrastructure, weak network segmentation, many admins, strong evidence burden |
| PSP or large merchant likely needing ROC | $60,000-$250,000+ | QSA-led assessment, ROC, multiple interviews/workstreams, testing, broad remediation, formal governance | Multi-tenant systems, processor integrations, many entities, complex change control |
Reducing spend starts with design choices made before the audit. Exploring Akurateco’s guide to PCI DSS v4.0 implementation is a useful starting point for teams comparing build-vs-buy paths.
How to Reduce PCI DSS Cost Without Lowering Security
The biggest PCI savings usually come from architecture decisions, not from cutting corners on security. When companies reduce how much card data their systems touch, isolate the environments that stay in scope, and rely on compliant infrastructure where it makes sense, they often lower assessment effort, testing burden, and ongoing operational costs at the same time.
1. Prioritize scope reduction
The strongest lever is scope reduction. Keep raw card data out of your systems wherever possible. Use a hosted payment page, outsourced payment collection, isolated payment components, or provider-managed token services where that fits your business model.
PCI SSC’s FAQ on SAQ A makes the principle clear: SAQ A can apply only when all payment-page elements that capture card data are delivered directly by a PCI DSS validated third-party service provider. That is why architecture matters so much. It is not enough to “embed payments somehow.” The browser path matters.
2. Use tokenization to shrink the CDE
Tokenization is not magic, but it is powerful. PCI SSC’s tokenization guidance says tokenization can affect PCI DSS scope. To put it simply, fewer systems handling real card data usually means fewer systems to secure, test, and evidence.
3. Segment aggressively
Good network segmentation does not eliminate PCI obligations, but it can stop your CDE from swallowing neighboring systems. That reduces testing scope, narrows evidence collection, and lowers the blast radius of change. PCI SSC’s modern scoping and segmentation guidance exists because this remains one of the highest-value architecture decisions in PCI programs.
4. Buy compliant infrastructure where it makes sense
Use a PCI-compliant platform where it makes sense. Akurateco offers a PCI DSS-compliant platform and handles obtaining and renewing PCI certification for the platform itself, which can reduce the compliance burden on customers by shrinking the amount of infrastructure, testing, and evidence they need to manage directly.
That does not eliminate PCI obligations altogether, though. Scope reduction does not make compliance disappear. Merchants still remain responsible for areas such as website security, vendor oversight, access control, evidence collection, and confirming the correct validation path with their acquirer or payment brands.
PCI DSS 4.x Budget Impacts You Shouldn’t Miss
In 2026, many surprises come from teams that budgeted for old habits while assessing against v4.x realities.
The largest example is the March 31, 2025 milestone. PCI SSC says the future-dated requirements were treated as best practices until that date, and are now required in assessments.
For web merchants, the biggest new budget line is often payment-page security. PCI SSC says Requirements 6.4.3 and 11.6.1 require payment-page scripts to be authorized, integrity-checked, and monitored for tampering, along with relevant security-impacting headers. That may require new tooling, documented script inventories, change controls, and evidence that the controls are continuously operating.
There are also softer cost impacts, like broader control of ownership between app, infra, and security teams, more evidence requests, more recurring reviews, and more effort around authentication, including MFA in the right places.
Practical Checklist: Estimate Your PCI Cost in 30 Minutes
Before asking, “How much will PCI cost us?”, it helps to answer a simpler question first: what exactly are we paying to secure, test, document, and maintain? A quick scoping exercise will not give you a final quote, but it will help you build a much more realistic budget range and spot the cost drivers early.
Use this checklist to pressure-test your likely PCI spend.
1. Map your payment flows
Start by defining the payment flows you actually run today. Look at whether the business operates as e-commerce only, subscription-based, omnichannel, or as a PSP, and identify where customers enter card data on your site, inside an iframe, through a hosted payment page, or elsewhere. This matters because PCI cost depends heavily on how card data moves through your environment, not just on transaction volume.
2. Identify where cardholder data touches your environment
Next, determine whether you store, process, or transmit cardholder data anywhere in your stack, and if so, where. It is important to distinguish between handling raw PAN data and working only with tokens. You should also identify which applications, APIs, servers, databases, browser-side scripts, and support tools are involved. The more places cardholder data appears, the more systems are likely to fall into scope.
3. Count what sits inside the CDE
Once you understand the payment flow, count the assets inside or connected to the cardholder data environment (CDE). This usually includes payment-facing applications, servers, databases, cloud services, domains, privileged accounts, and third-party integrations. A larger CDE almost always means higher cost across validation, testing, and evidence collection.
4. Estimate your likely validation path
At this stage, try to determine which validation route is most likely to apply. Consider which SAQ type you may be eligible for, whether your environment could require a QSA-led assessment and possibly a ROC, and whether your architecture truly qualifies for a lighter validation path. This question alone can significantly change the budget.
5. Check whether recurring testing applies
Budgeting is incomplete until you understand your recurring testing obligations. You should confirm whether internet-facing in-scope systems require ASV scans, whether an annual penetration test is needed, and how many applications, APIs, environments, or external assets that testing would cover. Since testing is one of the most common recurring PCI costs, it should be estimated early.
6. Review all vendors that touch payment data
Review every vendor or provider that interacts with cardholder data or affects the payment flow. This often includes PSPs, gateways, tokenization providers, hosted payment page providers, fraud tools, support platforms, and cloud or infrastructure vendors.
For each one, check whether it falls into scope, whether it can provide clear PCI documentation and compliance artifacts, and whether it can support your evidence package during validation. Weak vendor documentation often increases internal workload and delays the assessment process.
7. Check which PCI DSS v4.x requirements may increase cost
This is where many teams underestimate effort. Review whether newer PCI DSS v4.x requirements will affect your stack, especially around e-commerce script security, monitoring for tampering, MFA scope, and broader evidence and control validation expectations. If your payment flow depends on browser-side scripts or distributed web teams, these requirements can increase tooling, monitoring, and documentation costs.
8. Add a remediation reserve
Finally, assume that at least some gaps will be found. Estimate what it would take to fix logging weaknesses, access-control issues, outdated components, or poor segmentation, and whether that would require new tooling, engineering time, or outside support. This is often the most overlooked budget item, even though it is one of the biggest real cost drivers.
A simple budgeting formula
A practical first estimate looks like this: validation, testing, remediation reserve, and internal labor = your realistic PCI budget. That will not replace a formal assessment, but it will give you a much better starting point than treating PCI as a single audit invoice. For more operational guidance, Akurateco’s article on managing PCI DSS compliance gives a useful starting point.
Conclusion
The real PCI DSS cost is never just an auditor invoice. It is the cost of scope, architecture, testing, remediation, and recurring control ownership.
The fastest way to lower it is usually not negotiating harder with assessors. It is reducing the scope before the assessment begins. A cleaner architecture, stronger vendor boundaries, and a smarter tokenization strategy can shrink both validation effort and ongoing operations.
Teams that want to reduce cost and time-to-compliance should start with infrastructure choices.
FAQ
What is included in the PCI DSS cost?
It includes validation work, documentation, scans, penetration tests, security controls, internal labor, evidence collection, and ongoing operations. For many teams, remediation and recurring control ownership cost more than the assessment itself.
Is the SAQ cost always cheap?
No. Public market ranges are broad because SAQ effort depends on scope, the right SAQ type, evidence quality, and how much outside help you need. On average, SAQ support is around $50 to $10,000.
When do you need a Qualified Security Assessor (QSA) and a Report on Compliance (ROC)?
Typically, when you are a Level 1 merchant, a larger or more complex service provider, or your acquirer/payment brands require a formal assessment. PCI SSC maintains separate ROC templates for QSA-led validation, while SAQs remain for eligible self-assessing entities.
How much does an ASV scan typically cost per year?
A common public planning range is about $400 to $2,000 per year for straightforward environments, based on $100 to $500 per quarter. SecurityMetrics also lists a $150 quarterly product example.
Why did PCI DSS v4.x increase effort for some e-commerce teams?
Because the formerly future-dated items became required after March 31, 2025, and PCI SSC’s payment-page requirements now focus on script authorization, integrity checks, and tamper monitoring. That adds tooling, process, and evidence burden.
What is the fastest way to reduce PCI costs?
Use architecture to reduce scope: hosted checkout, clean vendor boundaries, tokenization, and strong segmentation. The goal is to keep as much of your stack as possible out of direct card-data handling while still meeting your obligations.
Does using a PCI-compliant platform eliminate PCI requirements for me?
No, it doesn’t remove your PCI obligations entirely, because your business is still responsible for the parts of the payment flow, access, website, vendors, and operations that remain under your control. However, using a PCI-compliant platform like Akurateco can reduce scope and make compliance easier by lowering how much payment infrastructure and evidence you need to manage yourself.






